Wireless Password Recovery 6.8
Wireless Password Recovery retrieves passwords for wireless networks
Program info
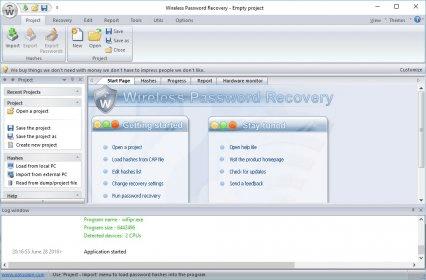
Wireless Password Recovery can help you assess the security of wireless networks and retrieve passwords. Due to the complexity of these types of operations, the utility may seem difficult to use for inexpert users at first. In spite of this, its interface is rather straightforward. Besides, its design is very similar to that of Microsoft Office products, which definitely helps flattening its learning curve. It can also be customized with various themes.
The tool has a series of features that allow recovering passwords. Besides, it supports different types of password-recovery methods. From the group of the so-called smart attacks, which are supposed to be faster, you can choose from Preliminary, Artificial Intelligence and Fingerprint. There´s also another group comprising common attacks, such as Brute Force, Dictionary and Mask. A third group is made up of advanced attacks, including Base Word, Combined Dictionary, Phrase Attack and Hybrid Dictionary. Finally, you can also use Batch Attack, which is a user-defined combination of some of the above mentioned methods.
Recovering passwords can take a lot of time using the hardware resources available from a standard machine. Luckily, this application can exploit all your computer´s potential as it can make use of not only your CPU but also your GPU to shorten the waiting time.
In general, Wireless Password Recovery is not intended for home users. Instead, it is for security auditors, network administrators and data forensics experts who can benefit the most from its use. If you have difficulties to use it at first, it´s logical. However, I’m sure you’ll overcome them with the help of the accompanying help files. Regrettably, I must say that they contain some typos, and some pages have not been edited well because they are written in Latin.
Pros
- It uses several types of password-recovery attacks, some of them unique
- It can use all your computer’s processing power
- It lets you create advanced audit reports
- On-the-fly decryption of hashes
Cons
- It is difficult to use at first
- Its help files need revising
Details
Extensions

No information available
The data will be available later.